Corporate Events
New Trends
Latest News
Our Blog

Your Packaging Is Talking to Customers. What Is It Saying?
Every business obsesses over its logo, its website and its ads. Yet one of the most powerful branding tools is often treated as an afterthought: the packaging the product actually arrives in. In a crowded market, that is a missed opportunity. Packaging is communication, whether …

What Fleurs de Villes FLORA Just Showed Toronto Couples About Wedding Flower Styles
Every spring, Toronto’s engaged couples do what engaged couples have always done: scroll endlessly through photographs of other people’s weddings, flag what they like, and try to translate it into something a florist can actually quote. What changed this May is that they had a …

Singapore Manufacturers Face Automation Cliff: Training Budgets Double as Workforce Pivots from Assembly to Robotics
Singapore’s manufacturing sector is undergoing its most dramatic transformation since the electronics boom of the 1970s. The city-state’s factories are deploying robots at the second-highest rate globally—730 robots per 10,000 workers according to Singapore’s Economic Development Board—and the humans who used to do those jobs …
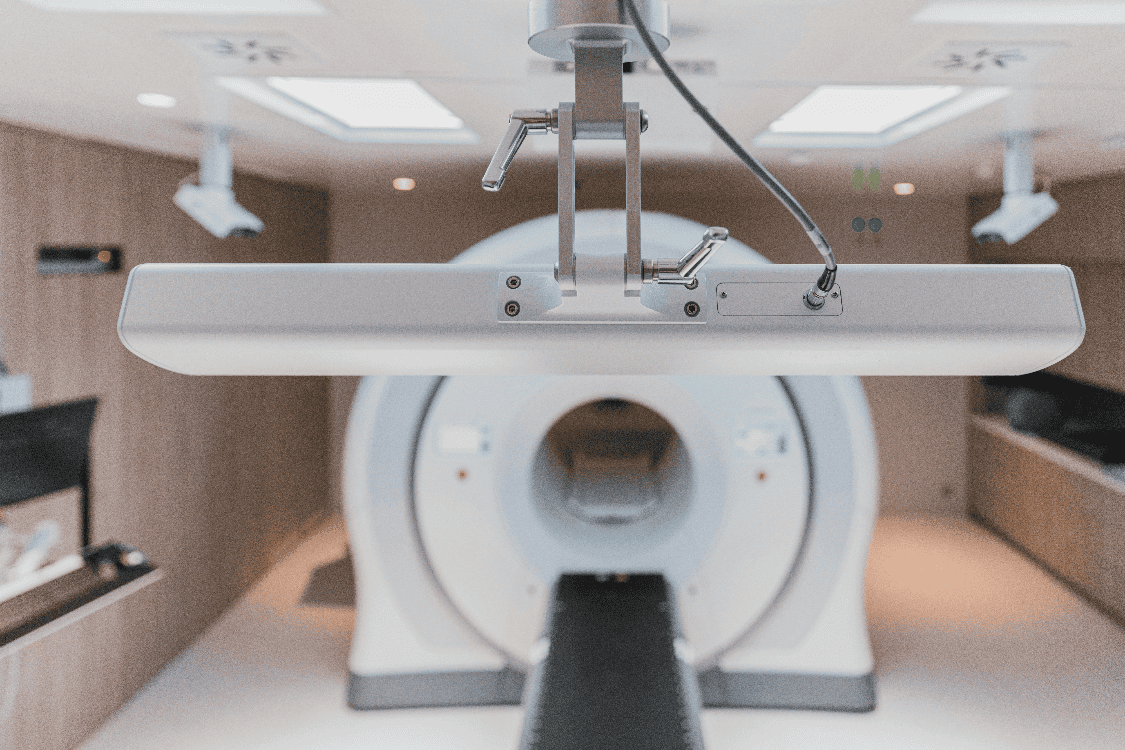
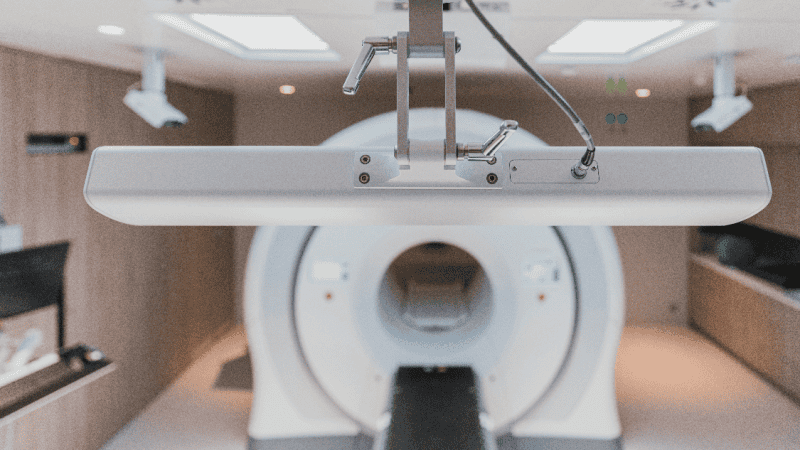
5 AI Innovations That Are Shaping the Future of Imaging Centers
Imaging centers are changing fast as artificial intelligence becomes part of routine care. Machine models now play a role in how scans are acquired, reconstructed and triaged, and those shifts affect technologists, radiologists and patients. Faster throughput and higher image clarity are visible outcomes, while …

How to Use Native Plants for a Sustainable Landscape
Native plants anchor a resilient approach to greener outdoor areas. They fit local soils and climates and often need far less water and care than exotic options. Choosing them can cut maintenance time while creating habitat for local birds and pollinators. The goal here is …

Understanding Precious Metals as a Long-Term Investment
Precious metals have been a store of value across many generations and remain a topic of interest for long term savers and investors. Their physical nature gives a sense of permanence that paper claims cannot match, while price action reflects a mix of supply limits, …

How Litigation Lawyers Protect Your Reputation and Business
Reputation can be as important as revenue when a firm faces serious claims that threaten trust and market position. Litigation lawyers move quickly to protect the public story about a company while keeping internal operations steady and focused. Their methods combine legal know how and …

5 Smart Portfolio Moves Using Precious Metals Wisely
Precious metals can play a constructive role in a thoughtful investment plan, offering texture and ballast when other assets waver. Many investors turn to gold and silver to calm nerves and protect purchasing power during turbulent periods in markets. Investors exploring finance strategies using precious …

Are Waffle Stick Makers Easy to Operate? Find Out Now
Waffle stick makers promise fast fun in the kitchen and an easy way to serve breakfast or snacks to a crowd. Operating one looks simple at first glance and many models aim for a plug and play feel that lowers the barrier for a casual …

Can Smart Thermostats Improve Air Conditioning? Discover Why
Smart thermostats bring a fresh take on keeping indoor temperature in check and can change how air conditioning is used in many homes. These devices learn patterns, respond to presence, and let people adjust settings from a phone without running back to a control panel …